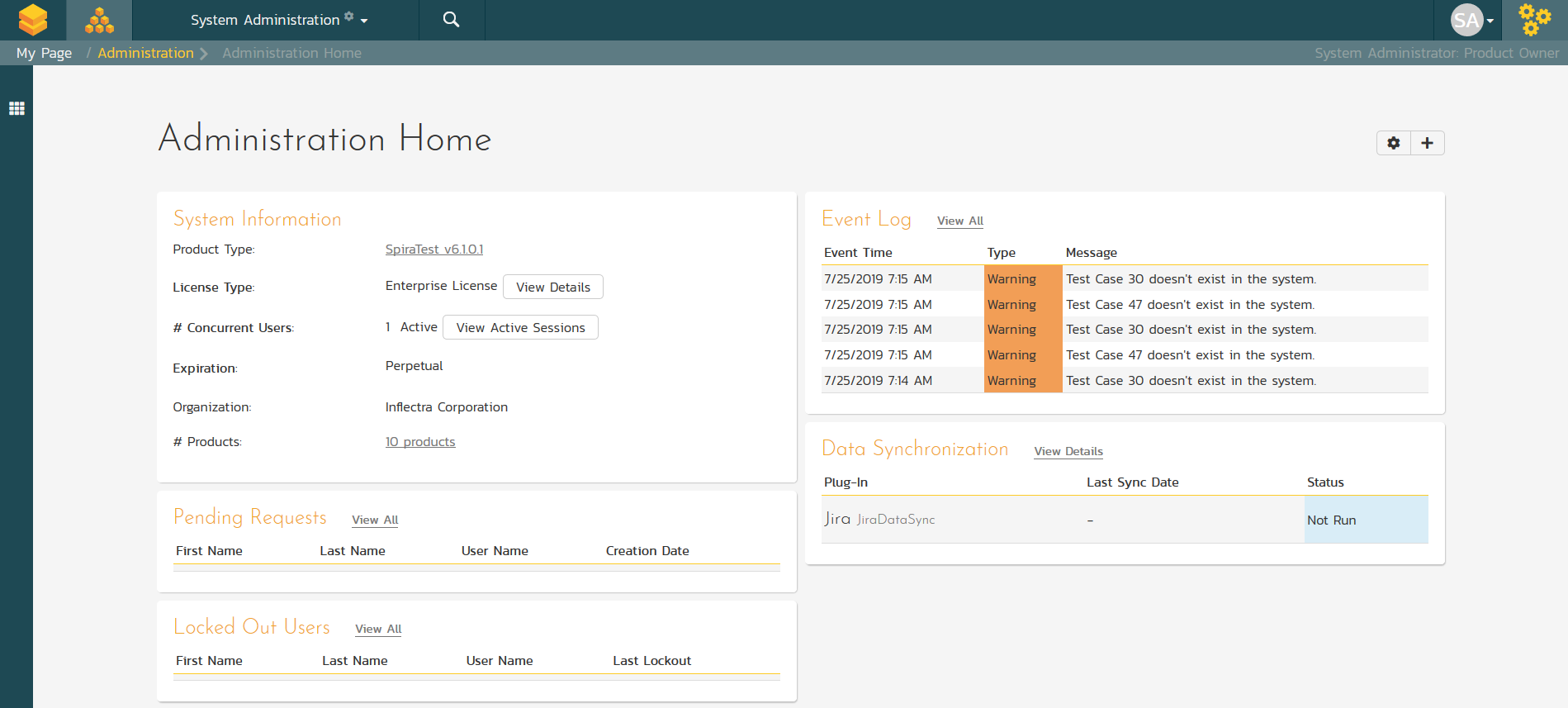
System Administration
SpiraTest can be fully administered and maintained using only a web browser. With SpiraTest, there is no need to install complicated software or have IT staff involved every time you wish to create new project or add a user to the system.
This is the same regardless of whether you are deploying on-premise or in our cloud environment. SpiraTest allows you to easily create, edit, copy, and delete projects using a web-based interface. In addition you have the option of creating a new project using the customized settings of an existing template project.
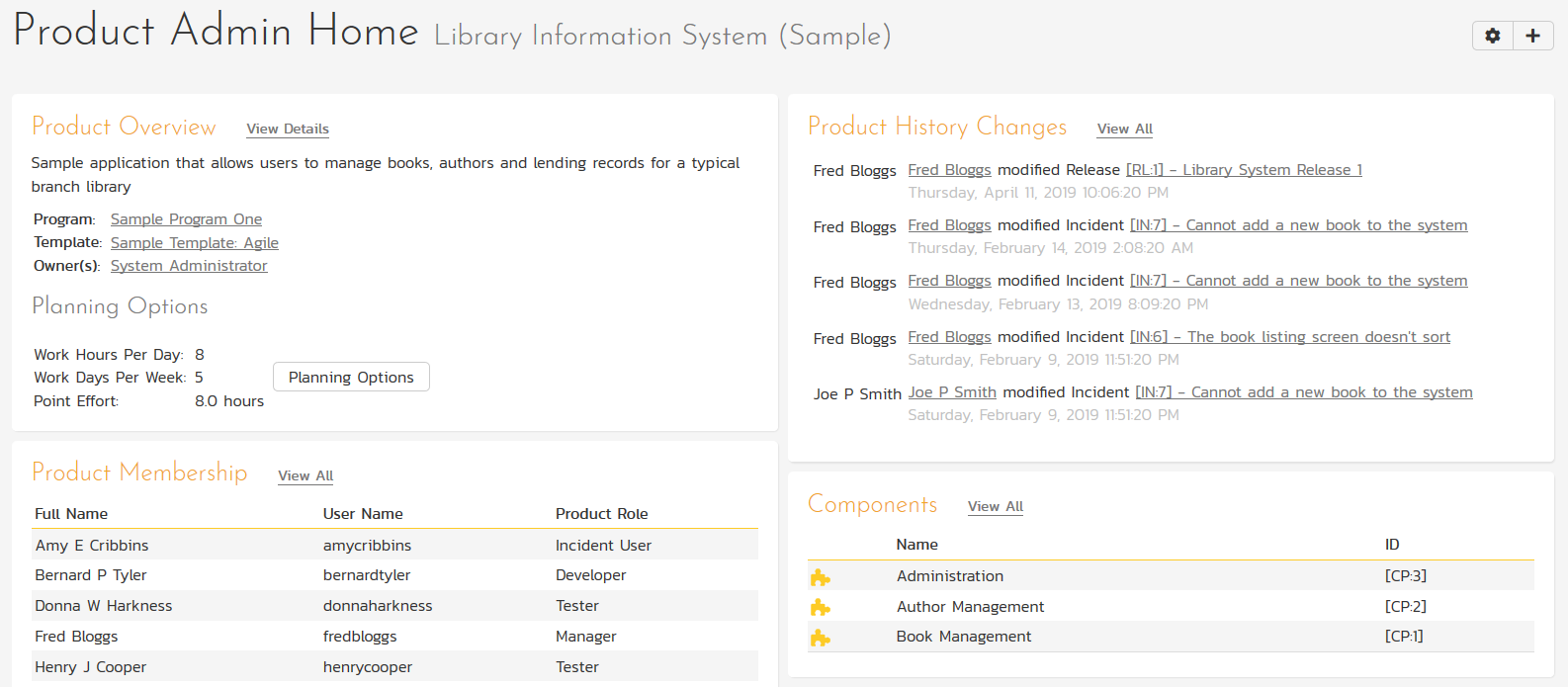
Product Administration
You can delegate administrators of SpiraTest to reduce the burden on your system administrators. That way each project have a set of owners that configure the projects, setup workflows and perform other project administrative tasks on a self-service basis:
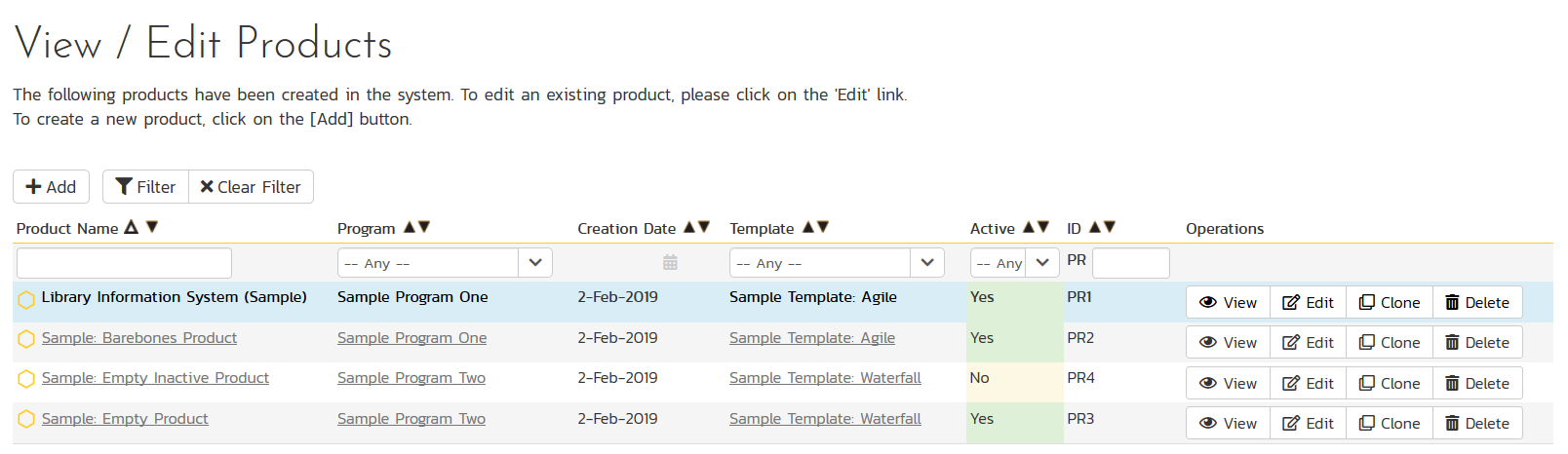
Template Administration
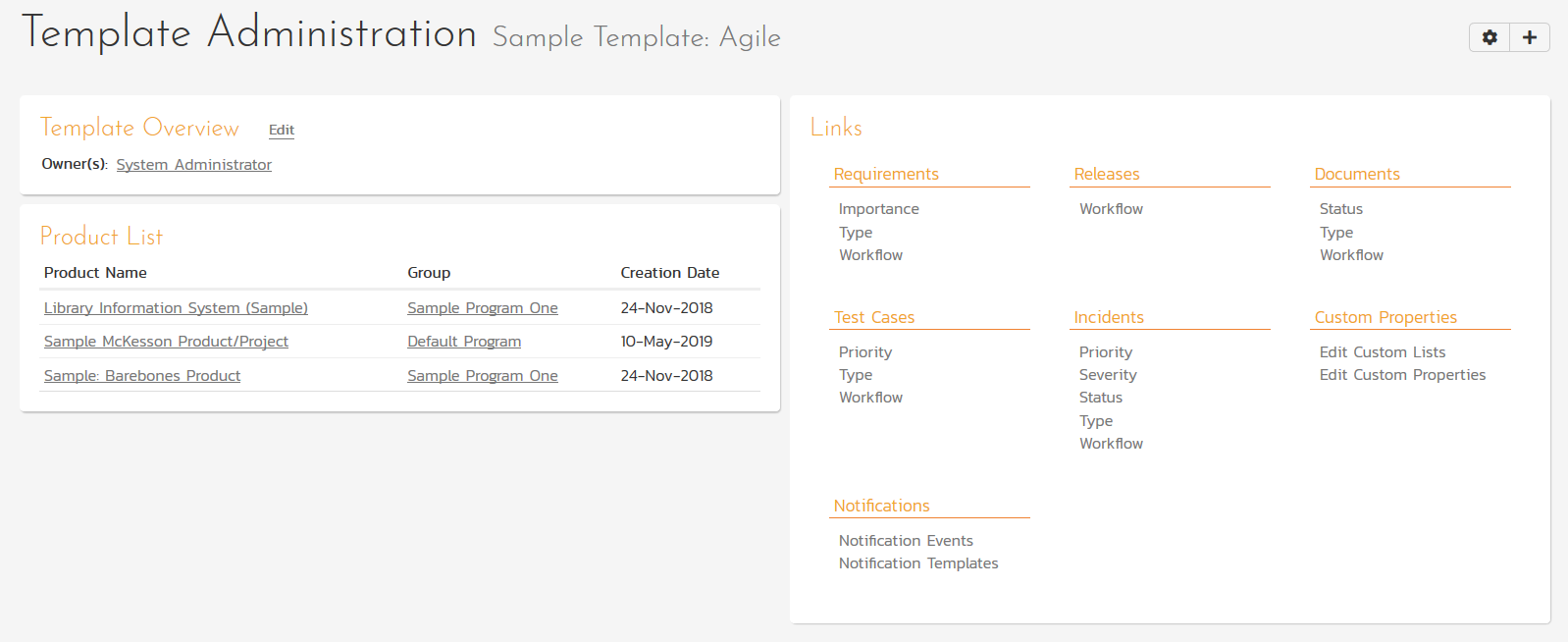
SpiraTest allows you to define reusable templates that each of the products in the system can be assigned to. This lets you define custom fields, configure the workflows and artifact fields for a single template that is then used by multiple products:
Within each template, the owners can customize the priorities, statuses, types, workflows, custom properties, email notifications and other settings:
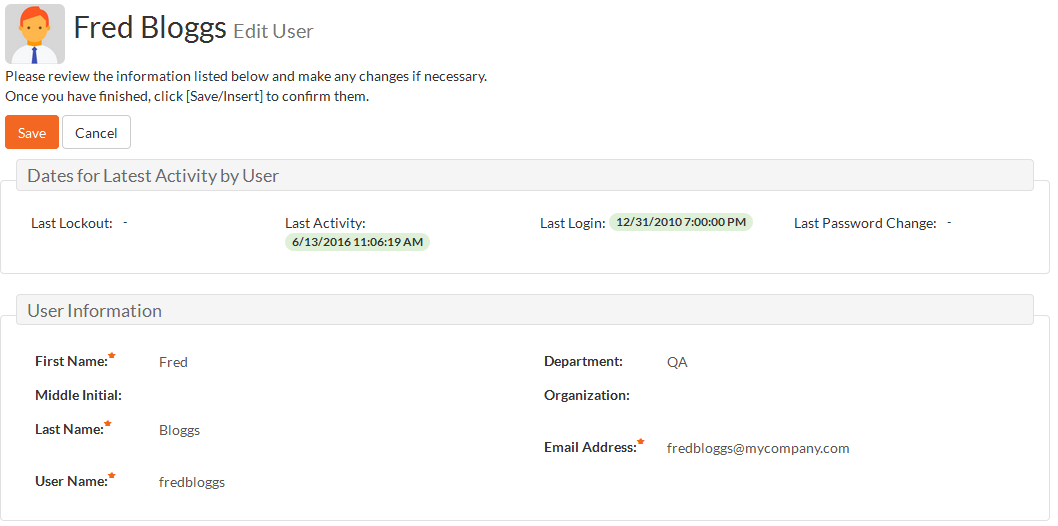
User Management
SpiraTest allows you to easily create, approve and manage user accounts. In addition you can link SpiraTest to any LDAP compatible directory server (e.g. Microsoft ActiveDirectory). Once imported, SpiraTest will authenticate those users against that server, removing the need for users to manage passwords in multiple places.
For ultimate flexibility you can have a combination of LDAP-based users and SpiraTest managed users (e.g. for external vendors and partners).
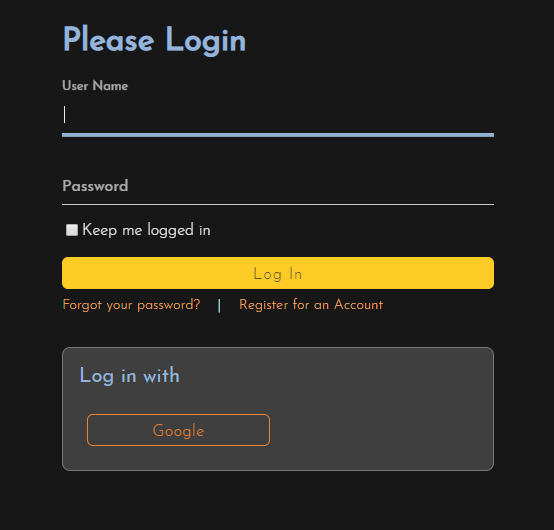
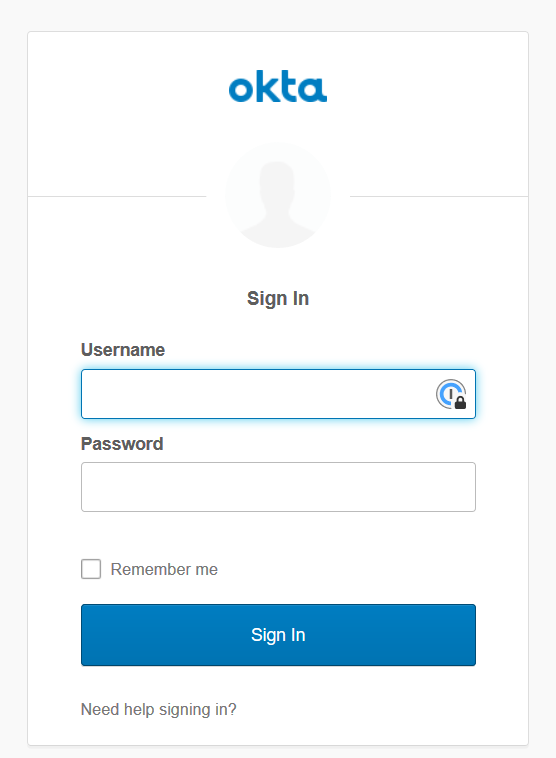
Single Sign On (SSO) With OAuth
When you login to SpiraTest, you normally enter in a login and password that is managed and stored specifically by SpiraTest internally. However, for larger enterprises, there is often a desire to centralize (for security and compliance reasons) the users that can access the various IT systems in the organization, and to have a central place to manage passwords and whether a user is allowed to access a specific system. When you enable OAuth support in SpiraTest, your users will be given the option of logging on using an external "provider" such as Google, Okta, Microsoft ADFS, or Azure AD.
When the user logs in with the external provider, they will be redirected to a web page belonging to that system instead. They will then login using this Single Sign On provider and if successful, will be redirected back to their normal home screen in SpiraTest.
SpiraTest supports the following OAuth Single Sign On providers:
- Microsoft Active Directory Federation Services (ADFS)
- Microsoft Azure Active Directory (Azure AD)
- Okta
- GitLab
- GitHub
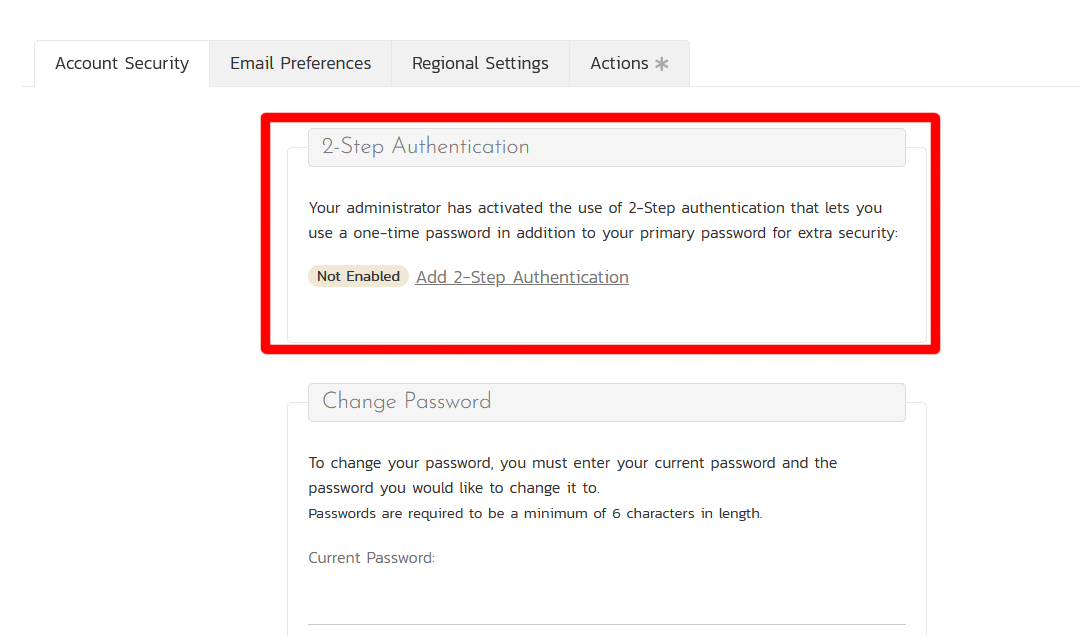
Multi-Factor Authentication (MFA)
Multifactor authentication (MFA) is a security technology that requires multiple methods of authentication from independent categories of credentials to verify a user's identity for a login or other transaction. Multifactor authentication combines two or more independent credentials: what the user knows, such as a password; what the user has, such as a security token; and what the user is, by using biometric verification methods.
SpiraTest supports MFA on all users accounts that are not managed by a Single Sign On provider, including those using SpiraTest authentication or LDAP-based authentication.
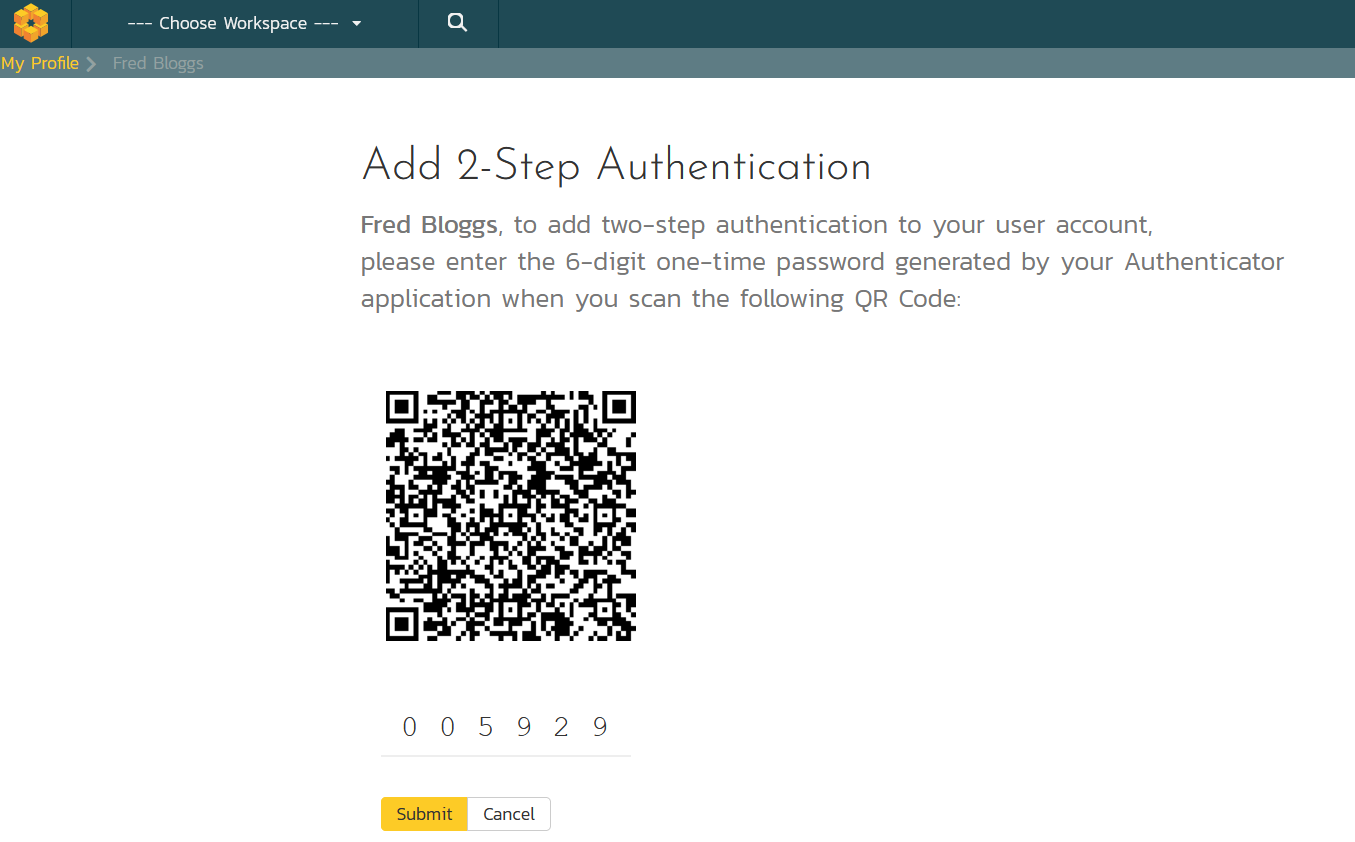
Users can choose to add MFA to their user profile, after which they will be shown a special QR Code that they need to scan with their authenticator application.
Once the code is scanned and the sample one time password verified, they will in future need to provide a special, randomly generated one-time password in addition to their username and primary SpiraTest password:
Testing Settings
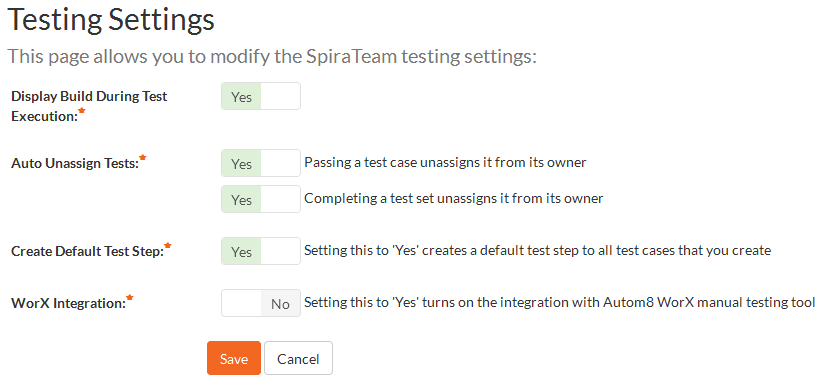
SpiraTest is designed to have sensible out of the box default options to make deployment easy, but for more advanced users, you can configure the behavior of the testing functionality:
System Configuration
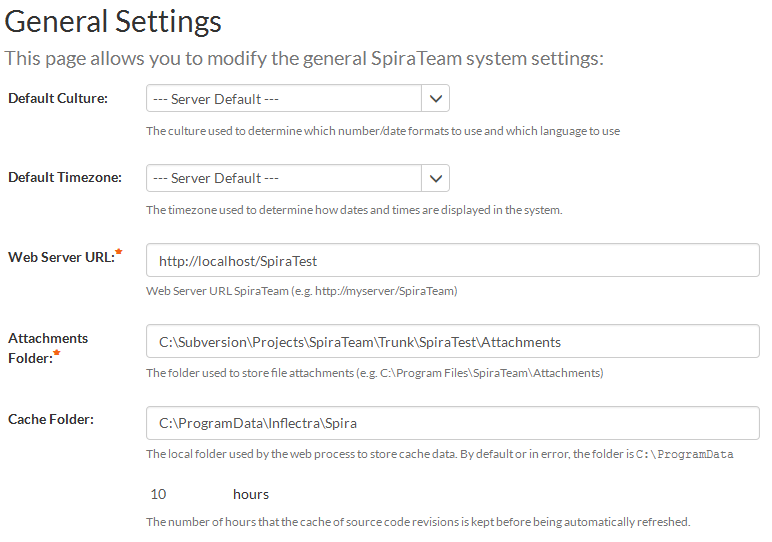
SpiraTest is designed to fit into your enterprise environment and support your enterprise IT policies. It gives the administrator control of the default timezone and region/language settings as well as the retention period for log messages and other configuration data:
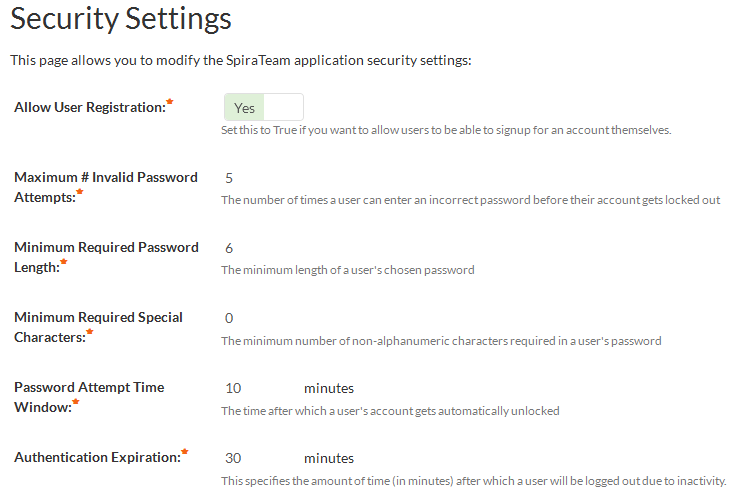
SpiraTest also allows you to configure the security settings to meet your IT security policies:
Try SpiraTest free for 30 days, no credit cards, no contracts
Start My Free TrialAnd if you have any questions, please email or call us at +1 (202) 558-6885